Online Banking Login
Banking Safety Center
Excursion Visa
GO PLACES. DO MORE THINGS.
Experience more of life with our new Excursion™ Visa Signature®
Transfer Now
External transfers available in online & mobile banking
- Log in to your online banking to get started today!
Business Mobile
Business banking made easier with our mobile app!
- Check Balances
- Review Transactions
- Make Transfers
- Send Payments
- Deposit Checks
- Fraud Protection
Rewards Credit Card
GREAT RATES. REWARDS. SECURITY.
The credit card from the bank you know best.
- Personal Service with Worldwide reach
- Better reward points
- Competitive Rates with Hometown Service
- More Security
GSB Card Control
Take control of your debit card with GSB card control
- Quickly detect unauthorized activity on your debit card
- Turn your debit card off and on
- See your account balance
- Find nearby ATMs
- Submit travel notices
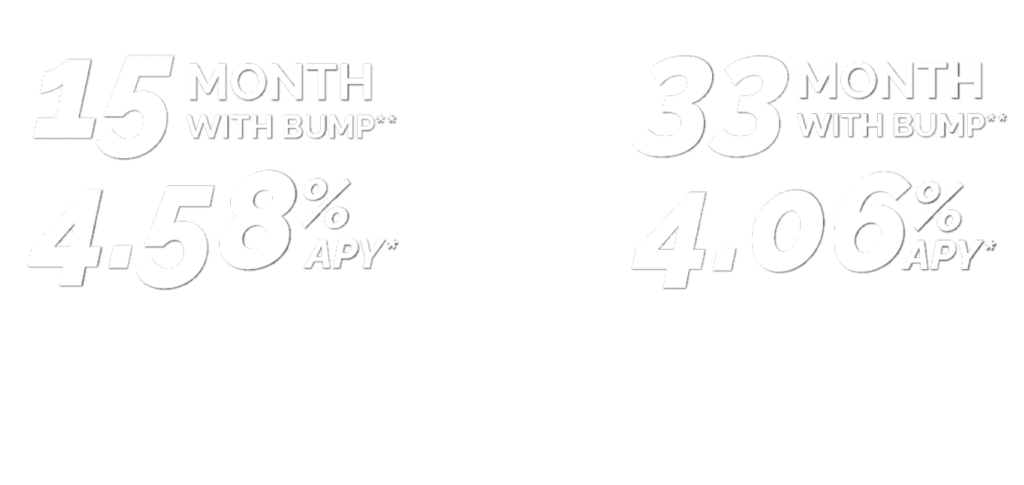
Simply Savings
SIMPLY SAVINGS
Let your money do the work
for you & earn more today!
- Low Minimums
- No Lengthy Requirements
- Easy Access to Your Money

Grinnell State Bank Locations



1101 Court Ave
Marengo, IA 52301
(319) 642-5511 | Bank
(319) 642-5514 | Insurance

BANKING ON THE GO
Convenient Online & Mobile Banking
Check out all of our options that make banking fit into your life.


NOT A CUSTOMER YET?
Get Started! Open your accounts in just 15 minutes.
- Financial Advisors, Loan Officers & Insurance Agents working under the same roof.
- MasterCard Debit Cards
- No Monthly Fees on Debit Cards
OUR BEST ACCOUNTS BUNDLED
Simply Switch
The best accounts bundled to make your banking experience simple.
Combine the smarter way to save with the convenience of the no minimum average balance checking with our Simply Savings and Simply Checking accounts.

Grow Your Savings
With Simply Savings, simply deposit your money and save higher than the FDIC national average savings rate on up to $25,000. Enjoy high-yield savings without the term limits.

No Minimum Average Balance
With Simply Checking, dipping below your average account balance doesn’t result in enormous fees. With monthly service fees as low as $0.50 per month, you can enjoy your money your way.

Upgrade To Save On Fees
With Preferred Checking, you can wave (waive) monthly service fees goodbye by maintaining the Average Available (collected) Balance! Learn more about how to enjoy your money and make your accounts work for you with preferred checking. *Inactivity fees may still apply.

Simply Smarter Business
Simply Savings for business…don’t take it “personal”!
A savvy, high-yield business savings account that offers your business the ability to start earning a higher interest rate, higher than the FDIC national average savings rate, on your excess funds with an interest rate tiered based on your account balance. Learn more about our high yield business savings account.

GRINNELL WEALTH MANAGEMENT
Here to be your partner on your financial journey.
Whether you’re looking to invest, needing advice about how to save, or wanting a comprehensive look at your finances, we have the services & products backed by a team of advisors with over 78 years of combined experience, we will work with you to meet your financial goals.
- 24/7 Access to the Investment Platform
- Knowledgeable advisors, each with many years of experience
- A Financial Planning Tool you can use anywhere
- Performance Reviews at Request
Give us a call at 641.260.2GWM or click below to learn more.
Investment products are not FDIC insured, are not bank guaranteed, and may lose value.

EXCEPTIONAL CUSTOMER SERVICE
Real Humans Answer Your Calls
Imagine big bank products and services without those irritating automated phone prompts. Grinnell State Bank is proud to offer customer service with the small-town touch. Talk to you soon!